To start a transaction in CLISH use ***start transaction***.
Commands - ***commit***, or ***rollback*** to be used to end the transaction mode. All changes made using commands in transaction mode are applied at once or none of the changes are applied based on the way transaction mode is terminated.
#### Show Commands| **save config** | save the current configuration |
| **show commands** | shows all commands |
| **show allowed-client all** | show allowed clients |
| **show arp dynamic all** | displays the dynamic arp entries |
| **show arp proxy all** | shows proxy arp |
| **show arp static all** | displays all the static arp entry |
| **show as** | displays autonomous system number |
| **show assets all** | display hardware information |
| **show bgp stats** | shows bgp statistics |
| **show bgp summary** | shows summary information about bgp |
| **show vrrp stats** | show vrrp statistics |
| **show bootp stats** | shows bootp/dhcp relay statistics |
| **show bootp interface** | show all bootp/dhcp relay interfaces |
| **show bonding groups** | show all bonding groups |
| **show bridging groups** | show all bridging groups |
| **show backups** | shows a list of local backups |
| **show backup status** | show the status of a backup or restore operation being performed |
| **show backup last-successful** | show the latest successful backup |
| **show backup logs** | show the logs of the recent backups/restores performed |
| **show clock** | show current clock |
| **show configuration** | show configuration |
| **show-config state** | shows the state of configuration either saved or unsaved |
| **show date** | shows date |
| **show dns primary** | shows primary dns server |
| **show dns secondary** | shows secondary dns server |
| **show extended commands** | shows all extended commands |
| **show groups** | shows all user groups |
| **show hostname** | show host name |
| **show inactivity-timeout** | shows inactivity-timeout settings |
| **show interfaces** | shows all interfaces |
| **show interfaces ethx** | shows settings related to an interface “x |
| **show interfaces** | show detailed information about all interfaces |
| **show ipv6-state** | shows ipv6 status as enabled or disabled |
| **show management interface** | shows management interface configuration |
| **show ntp active** | shows ntp status as enabled or disabled |
| **show ntp servers** | shows ntp servers |
| **show ospf database** | shows ospf database information |
| **show ospf neighbors** | shows ospf neighbors information |
| **show ospf summary** | shows ospf summary information |
| **show pbr rules** | shows policy based routing rules |
| **show pbr summary** | shows policy based routing summary information |
| **show pbr tables** | show pbr tables |
| **show route** | shows routing table |
| **show routed version** | shows information about routed version |
| **show snapshots** | shows a list of local snapshots |
| **show snmp agent-version** | shows whether the version is v1/v2/v3 |
| **show snmp interfaces** | shows snmp agent interface |
| **show snmp traps receivers** | shows snmp trap receivers |
| **show time** | shows local machine time |
| **show timezone** | show configured timezone |
| **show uptime** | show system uptime |
| **show users** | show configured users and their homedir, uid/gid and shell |
| **show user <username>** | shows settings related to a particular user |
| **show version all** | shows version related to os edition, kernel version, product version etc |
| **show virtual-system all** | show virtual-systems configured |
| **show vpn tunnels** | use to show the vpn tunnels |
| **show vrrp stats** | shows vrrp status |
| **show vrrp interfaces** | shows vrrp enabled interfaces |
| **add allowed-client host any-host / add allowed-client host <ip address>** | add any host to the allowed clients list/ add allowed client by ipv4 address |
| **add backup local** | create and store a backup file in /var/cpbackups/backups/( on open servers) or /var/log/cpbackup/backups/ ( on checkpoint appliances) |
| **add backup scp ip value path value username value** | adds backup to scp server |
| **add backup tftp ip value \[ interactive \]** | adds backup to tftp server |
| **add snapshot** | create snapshots which backs up everything like os configuration, checkpoint configuration, versions, patch level), including the drivers |
| **add syslog log-remote-address <ip address> level <emerg/alert/crit/err/warning/notice/info/debug/all>** | specifies syslog parameters |
| **add user <username> uid <user-id-value> homedir** | creates a user |
| **expert** | executes system shell |
| **halt** | put system to halt |
| **history** | shows command history |
| **lock database override** | overrides the config-lock settings |
| **quit** | exits out of a shell |
| **reboot** | reboots a system |
| **restore backup local \[value\]** | restores local backup interactively |
| **rollback** | ends the transaction mode by reverting the changes made during transaction |
| **save config** | save the current configuration |
| **set backup restore local <filename>** | restores a local backup |
| **set cluster member admin {down | up}** | initiating manual cluster failover |
| **set core-dump <enable/disable>** | enable/disable core dumps |
| **set date yyyy-mm-dd** | sets system date |
| **set dhcp server enable** | enable dhcp server |
| **set dns primary <x.x.x.x>** | sets primary dns ip address |
| **set dns secondary <x.x.x.x>** | sets secondary dns ip address |
| **set expert-password** | set or change password for entering into expert mode |
| **set edition default <value>** | set the default edition to 32-bit or 64-bit |
| **set hostname <value>** | sets system hostname |
| **set inactivity-timeout <value>** | sets the inactivity timeout |
| **set interface eth*x* ipv4-address x.x.x.x mask-length 24** | adds ip address to an interface |
| **set ipv6-state on/off** | sets ipv6 status as on or off |
| **set kernel-routes on/off** | sets kernel routes to on/off state |
| **set management interface <interface name>** | sets an interface as management interface |
| **set message motd value** | sets message of the day |
| **set ntp active on/off** | activates ntp on/off |
| **set ntp server primary x.x.x.x version <1/2/3/4>** | sets primary ntp server |
| **set ntp server secondary x.x.x.x version <1/2/3/4>** | sets secondary ntp server |
| **set snapshot revert<filename>** | revert the machine to the selected snapshot |
| **set snmp agent on/off** | sets the snmp agent daemon on/off |
| **set snmp agent-version <value>** | sets snmp agent version |
| **set snmp community <value> read-only** | sets snmp readonly community string |
| **add snmp interface <interface name>** | sets snmp agent interface |
| **set snmp traps receiver <ip address> version v1 community value** | specifies trap receiver |
| **set snmp traps trap <value>** | set snmp traps |
| **set static-route x.x.x.x/xx nexthop gateway address x.x.x.x on** **set static-route x.x.x.x/xx comment "{comment}"** | adds specific static route comment static route |
| **set static-route *NETWORK\_ADDRESS/MASK\_LENGTH* nexthop gateway address *GATEWAY\_IP\_ADDRESS* off** **set static-route <Destination IP address> off** **set static-route default nexthop gateway address *GATEWAY\_IP\_ADDRESS* off** | Delete Routes |
| **set time <value>** | sets system time |
| **set time zone <time-zone>** | sets the time zone |
| **set vsx off** | sets vsx mode on |
| **set vsx on** | sets vsx mode off |
| **set user <username> password** | sets users password |
| **set web session-timeout <value>** | sets web configuration session time-out in minutes |
| **set web ssl-port <value>** | sets the web ssl-port for the system |
| Action | Use on | Command |
|---|---|---|
| SIC Reset | **GW / MGMT** | 1. ***cpconfig*** 2. ***Secure Internal Communication*** 3. ***re-initialize communication*** 4. ***Enter activation key*** ***On MGMT goto GW settings - General Properties - Communication and re-initialize the SIC with the provided activation key*** ***More information:*** ***[How to reset SIC](https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=sk65764)*** ***[How to troubleshoot SIC](https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=sk30579)*** ***[How to reset SIC on a VSX Gateway for a specific Virtual System](https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=sk34098)*** |
| Show licenses | **MGMT / GW** | ***cplic print -x*** (-x print signatures) |
| Remove Evaluation License | **GW** | ***cplic eval\_disable*** You have disabled Check Point evaluation period For activation you need to restart ALL Check Point modules (performing cpstop & cpstart) |
| Get licenses from management system on gateway | **GW** | ***contract\_util mgmt*** |
| Show enabled blades
Example:
\# enabled\_blades
fw ips ThreatEmulation Scrub | **GW** | **enabled\_blades** |
| ClusterXL Switch over (disable ClusterXL state) | **GW** | ***clusterXL\_admin down*** Note: The \[-p\] is an optional flag (stands for "permanent") \- the Critical Device called "admin\_down" will be automatically added to the $FWDIR/conf/cphaprob.conf file, so that this configuration survives the reboot. |
| Show Cluster status | **GW** | ***cphaprob stat*** |
| Show Virtual Cluster Interfaces | **GW** | ***cphaprob -a if*** |
| Debug to see all dropped connections | **GW** | ***fw ctl zdebug drop*** ***fw ctl zdebug -h (help)*** |
| Debug to see all NAT informations | **GW** | ***fw ctl zdebug + xlat*** |
| Debug to get a fast packet trace | **GW** | ***fw ctl zdebug + packet | grep -B 1 TCP |grep -B 1 "(SYN)"*** |
| See stats of number of connections | **GW** | ***cpstat fw*** |
| Connections load on the fw | **GW** | ***fw tab -s -t connections*** |
| Clear ALL connections on fw from the table (CAUTION!) | **GW** | **fw tab -t connections -x** |
| ClusterXL sync statistics to R80.10 ([sk34476](https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=sk34476)) ClusterXL sync statistics for R80.20 and higher ([sk34475](https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=sk34475)) | **GW** **GW** | ***fw ctl pstat*** **CLISH: show cluster statistics sync Expert: cphaprob syncstat** |
| Show connected SmartConsole clients | **MGMT** | ***cpstat mg*** |
| Manage the GUI clients that can use SmartConsoles to connect to the Security Management Server | **MGMT** | **cp\_conf client get** # Get the GUI clients list **cp\_conf client add <GUI client>** # Add one GUI Client **cp\_conf client del < GUI client 1> < GUI client 2>**... # Delete GUI Clients **cp\_conf client createlist < GUI client 1> < GUI client 2>**... # Create new list. |
| Show sync details | **GW** | ***fw ha -f all*** |
| Shows packets accepted, dropped, peak connections, and **top rule hits** | **GW** | ***cpstat blades*** |
| Use CLI commands over SIC from MGMT without password, used as example for "last chance" configs. | **MGMT** | ***cprid\_util (--help)***
```shell
Example Reset admin password without access to GW:
/sbin/grub-md5-crypt
cprid_util -server |
| Show interfaces, ip-addresses and subnet mask, used for a very good interface-overview. | **MGMT/GW** | ***fw getifs*** |
| Show installed hotfixes and releases | **GW** | ***cpinfo -y all*** |
| Create cpinfo file for sending to the support. Included are log files and fw table dump. The resulting file is compressed | **MGMT / GW** | ***cpinfo -Ddlzk -o /var/tmp/$HOSTNAME*** |
| Show statistics about accelerated traffic | **GW** | ***fwaccel stats -s*** |
| This command will list what interface is connected to what IRQ to what core. | **GW** | ***fw ctl affinity -l -v -r*** ***fw ctl affinity -s*** will subsequently allow you to set the values. |
| \*\*UNDOCUMENTED\*\* Show state and timeline of ClusterXL events in CLISH | **GW** | ***CLISH: show routed cluster-state detailed*** |
| Top 10 Source-IPs in connection table. You need to manual convert hex in ascii to get the ip, like so: 0a1f0af2 = 10.31.10.242. For the top 10 destinations, substitute $4 for $2 in the awk command. | **GW** | ***fw tab -u -t connections | awk '{ print $2 }' | sort -n | uniq -c | sort -nr | head -10*** |
| Log Diagnostic Report It will analyze the logs and give you a brief output of your Current Logging and Daily Average Logging rates. It will also produce a detailed output at */tmp/sme-diag/results/detailed\_diag\_report.txt* [https://community.checkpoint.com/t5/Logging-and-Reporting/R80-xx-equivalent-of-CPLogInvestigator-for-Log-Volume-and/td-p/46792](https://community.checkpoint.com/t5/Logging-and-Reporting/R80-xx-equivalent-of-CPLogInvestigator-for-Log-Volume-and/td-p/46792) | **LOG** | **$RTDIR/scripts/doctor\_log.sh** |
| Action | Use on | Command |
|---|---|---|
| VPN statistics | **GW** | ***cpstat -f all vpn*** |
| VPN Tunnel manipulation | **GW** | ***vpn tu*** Interactive usage (better): ***vpn shell*** |
| VPN Remote Access specific | **GW** | ***pep show user all*** |
| Check VPN-1 major and minor version as well as build number and latest hotfix. Use -k for kernel version | **GW** | ***vpn ver \[-k\]*** |
| Show, if any, overlapping VPN domains | **GW** | ***vpn overlap\_encdom*** |
| VPN IKE Debugging (P1 and P2 Communication) The resulting **$FWDIR/log/ike.elg** and/or **$FWDIR/log/ikev2.xml** can be used in the "IKEView" Utility from Check Point, see here: [sk30994](https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=sk30994) | **GW** | **vpn debug ikeon** (enable IKE debug) **vpn debug ikeoff** (disable IKE debug) |
| Action | Use on | Command |
|---|---|---|
| Show VSX status. Verbose with -v, interface list with -l or status of single VS with VS ID <id>. | **VSX / VS** | ***vsx stat \[-v\] \[-l\] \[id\]*** |
| Show connections stats
| **VSX** | **vsx stat -v -l** |
| View current shell context. | **VSX** | ***vsenv*** |
| Set context to VS ID <id> | **VSX** | ***vsenv <id>*** |
| Reset SIC for VS | **VSX** | ***vsenv <id>; fw vsx sicreset*** |
| View state tables for virtual system <id>. | **VSX** | ***vsenv <id>; fw tab -t <table>*** |
| View traffic for virtual system with ID <id>. Attention: with fw monitor use -v instead of -vs. | **VSX** | ***fw monitor -v <id> -e 'accept;'*** |
| View HA state of all configured Virtual Systems. | **VSX** | **cphaprob state** |
| View HA state for Virtual System ID <id>. | **VSX** | ***cphaprob -vs <id> state*** |
| Show all bond interfaces and Cluster state | **VSX** | **cphaprob show\_bond -a** |
| Check VS bit state | **VSX** | ***vs\_bits -stat*** All VSs are at 64 bits (R80.20 default, R80.10 need upgrade) |
| Show virtual devices memory usage | **VSX** | **cpstat -f memory vsx** |
| Traffic statistic per virtual system See [sk90860](https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=sk90860) More information: [Check Point Useful SNMP OIDs (VSX)](https://wiki.linuxnet.ch/bin/view/Vendors/Check%20Point/Operation/Check%20Point%20Useful%20SNMP%20OIDs%20%28VSX%29/) | **VSX** | ***snmpwalk -v 2c -c community 127.0.0.1 .1.3.6.1.4.1.2620.1.16.22.3 (*****vsxStatusMemoryUsage*)*** SNMPv2-SMI::enterprises.2620.1.16.22.3.1.1.1.0 = INTEGER: 0 SNMPv2-SMI::enterprises.2620.1.16.22.3.1.1.2.0 = INTEGER: 1 SNMPv2-SMI::enterprises.2620.1.16.22.3.1.1.3.0 = INTEGER: 2 SNMPv2-SMI::enterprises.2620.1.16.22.3.1.1.4.0 = INTEGER: 3 SNMPv2-SMI::enterprises.2620.1.16.22.3.1.2.1.0 = STRING: "vs0" SNMPv2-SMI::enterprises.2620.1.16.22.3.1.2.2.0 = STRING: "vs1" SNMPv2-SMI::enterprises.2620.1.16.22.3.1.2.3.0 = STRING: "vs2" SNMPv2-SMI::enterprises.2620.1.16.22.3.1.2.4.0 = STRING: "vs3" SNMPv2-SMI::enterprises.2620.1.16.22.3.1.3.1.0 = Gauge32: 0  SNMPv2-SMI::enterprises.2620.1.16.22.3.1.3.2.0 = Gauge32: 0  SNMPv2-SMI::enterprises.2620.1.16.22.3.1.3.3.0 = Gauge32: 0  SNMPv2-SMI::enterprises.2620.1.16.22.3.1.3.4.0 = Gauge32: 0  |
| To enable monitoring CPU per-VS with OID .1.3.6.1.4.1.2620.1.16.22.4 | **VSX** | **fw vsx resctrl monitor enable** |
| To enable monitoring memory per-VS with OID .1.3.6.1.4.1.2620.1.16.22.3 Needs a reboot! | **VSX** | **vsx mstat enable** |
To use the actual ssh login with mgmt\_cli use the undocumented feature `mgmt_cli -r true`
If your mgmt server is running on another port (ex. 8443) use `mgmt_cli --port 8443`
#### Show api-settings Check if clients are allowed to connect to the api and check all the api-settings. ``` mgmt_cli -r true --domain 'System Data' show api-settings ... accepted-api-calls-from: "all ip addresses" ... ``` #### API Status To confirm that the API is usable and available remotely, run the api status command. If Accessibility shows “Require all granted” it means that any system can access the API (on R80 this will show “Allow all”). ```shell [Expert@awsmgmt:0]# api status API Settings: --------------------- Accessibility: Require all granted Automatic Start: Enabled Processes: Name State PID More Information ------------------------------------------------- API Started 14472 CPM Started 14350 Check Point Security Management Server is running and ready FWM Started 13807 Port Details: ------------------- JETTY Internal Port: 50276 APACHE Gaia Port: 443 -------------------------------------------- Overall API Status: Started -------------------------------------------- API readiness test SUCCESSFUL. The server is up and ready to receive connections Notes: ------------ To collect troubleshooting data, please run 'api status -s| Research | SmartLog Query |
|---|---|
| Search for E-Mail Subject Note: Search without quotation marks and wildcard works for email\_subject | ***email\_subject:\*TEXT**\** |
| Application Control Proxy Log | ***blade:"Application Control" AND appi\_name:"Web Surfen" AND \*part-of-hostname**\** |
| Every logs of a specific rule | ***{ABC12345-ABC1-ABC1-ABC1-ABC123ABC12}*** |
| Security Management Log Server : when logs were not able to be sent to it | ***"were not sent to log server"*** |
| Filter Logs by Geo-Location | ***src\_country:"Germany" AND src:<ip-address>*** |
| Alert on GW | ***type:Alert AND origin:<fw-gwname>*** |
| FW Control Messages (Failover etc.) | ***type:Control*** |
| ClusterXL Control Messages, Cluster Switch over Messages | ***type:Control ClusterXL*** |
| DHCP Messages | ***service:dhcp*** |
| Address Spoofing | ***address spoofing*** |
| Find aggressive aging events | ***aggressive aging*** |
| Any TCP state errors listed in [sk101221](https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=sk101221&partition=Advanced&product=Security) | ***tcp (fin OR syn) NOT "both fin" NOT "established"*** In the query field, type "***tcp state***" (without quotes) or any relevant text (e.g., "***syn\_sent***", "***both fin***") |
| Global Broadcast | ***dst:255.255.255.255*** |
| HTTPS Inspection CRL or OCSP errors | ***blade:"HTTPS Inspection" crl OR ocsp*** |
| Certificates: any alert regarding crl (Certification Revocation List) or certificates (see [sk104400](https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=sk104400&partition=General&product=IPSec)for more details) | ***type:alert (certificate or CRL)*** |
| Potential network configuration problem messages in log - See [SK63160](https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=sk63160) | ***"Engine Settings - TCP"*** |
| IPS Bypass Messages See discussion here: [Checkmates: IPS bypass](https://community.checkpoint.com/thread/8884-ips-bypass) | ***blade:IPS NOT( action: (prevent OR block) ) OR "IPS Bypass Engaged" OR "IPS Bypass Disengaged"*** |
| Research | SmartLog Query |
|---|---|
| Threat Extraction | ***blade:"Threat Extraction" AND action:Extract*** |
| Threat Extraction Search for E-Mail Subject | ***blade:"Threat Extraction" OR blade:"Threat Emulation" AND email\_subject:" TTTTT" OR email\_subject:"TTTTT"*** |
| Threat Extraction show last activity | ***blade:"Threat Extraction" AND "Content Removal" OR "Conversion to PDF"*** |
| Threat Emulation show errors | ***blade:"Threat Emulation" \*"ended with verdict Error"\**** |
| Threat Emulation show found threats | ***blade:"Threat Emulation" AND severity:Critical NOT type:Correlated*** |
| Research | SmartLog Query |
|---|---|
| Seeing tunnels activities | ***tunnel\_test or action:"Key Install" or action:"Failed Log In" OR action:"Log In" OR action:"Log Out" OR action:reject OR action:Update*** |
| Connection Errors | ***blade:vpn AND action:Reject ( "endpoint" OR "user" OR "Office Mode" )*** |
| Errors Authenticating Users | ***"Could not obtain user object" "IKE failure"*** |
| Fan status | fanSpeedSensorStatus | .1.3.6.1.4.1.2620.1.6.7.8.2.1.6 |
| Power Supply status | powerSupplyStatus | .1.3.6.1.4.1.2620.1.6.7.9.1.1.2 |
| Raid status | raidDiskState | .1.3.6.1.4.1.2620.1.6.7.7.2.1.9 |
| Temperature status | tempertureSensorTable | .1.3.6.1.4.1.2620.1.6.7.8.1 |
| Connections | fwNumConn.0 | .1.3.6.1.4.1.2620.1.1.25.3.0 |
| Connections limit | fwConnTableLimit.0 | .1.3.6.1.4.1.2620.1.1.25.10.0 |
| ClusterXLState | haState | .1.3.6.1.4.1.2620.1.5.6.0 |
| CPUCores | multiProcUsage | .1.3.6.1.4.1.2620.1.6.7.5.1.5 |
| RAM - Real Total | memTotalReal64 | .1.3.6.1.4.1.2620.1.6.7.4.3 |
| RAM - Real Active | memActiveReal64 | .1.3.6.1.4.1.2620.1.6.7.4.4 |
| RAM - Real Free | memFreeReal64 | .1.3.6.1.4.1.2620.1.6.7.4.5 |
| RAM - Virtual Total | memTotalVirtual64 | .1.3.6.1.4.1.2620.1.6.7.4.1 |
| RAM - Virtual Active | memActiveVirtual64 | .1.3.6.1.4.1.2620.1.6.7.4.2 |
| Hmem fails | fwHmem-failed-alloc | .1.3.6.1.4.1.2620.1.1.26.1.21 |
| System Kmem fails | fwKmem-failed-alloc | .1.3.6.1.4.1.2620.1.1.26.2.15 |
| Swap memory utilization alert | chkpntSwapMemoryTrap | .1.3.6.1.4.1.2620.1.2000.4.1 |
| Real memory utilization alert | chkpntRealMemoryTrap | .1.3.6.1.4.1.2620.1.2000.4.2 |
| RAM - Memory Usage VS ID | vsxStatusMemoryUsageVSId | .1.3.6.1.4.1.2620.1.16.22.3.1.1 |
| RAM - Memory Usage VS Name | vsxStatusMemoryUsageVSName | .1.3.6.1.4.1.2620.1.16.22.3.1.2 |
| RAM - Memory Usage per VS | vsxStatusMemoryUsage | .1.3.6.1.4.1.2620.1.16.22.3.1.3 |
**URL Reputation** – for a domain/URL returns the classification and risk in accessing the resource **File Reputation** – for a file digest (md5/sha1/sha256/sha512) returns the risk in downloading the file without the need to scan it **IP Reputation** - for an IP address returns it’s classification and risk in accessing a resource hosted on it **Mail Security** – upload an email for scanning against malware and phishing attacks, based on award winning Sandblast engines
All APIs are RESTful, simple to use and can be integrated as part of a SOAR application, home-made application and more! Detailed API instructions including samples in Java/Python can now be found in the GitHub repository. Check it out here - [https://github.com/CheckPointSW/reputation-service-api](https://github.com/CheckPointSW/reputation-service-api) ### Swagger UI to explore the API [https://app.swaggerhub.com/apis-docs/cp-devops-cloud/reputation-service](https://app.swaggerhub.com/apis-docs/cp-devops-cloud/reputation-service) # GAIA - Easy execute CLI commands on all gateways simultaneously ### Link [https://community.checkpoint.com/t5/Enterprise-Appliances-and-Gaia/GAIA-Easy-execute-CLI-commands-on-all-gateways-simultaneously/m-p/50883](https://community.checkpoint.com/t5/Enterprise-Appliances-and-Gaia/GAIA-Easy-execute-CLI-commands-on-all-gateways-simultaneously/m-p/50883) # Threat Prevention Cyber Attacks Dashboard Template If you have Anti-Bot, Anti-Virus, IPS, Threat Emulation Blades active and a SmartLog License, you're maybe interested to see the following Dashboard: [](https://doc.gecloud.ch/uploads/images/gallery/2020-11/image-1604935138774.png) [](https://doc.gecloud.ch/uploads/images/gallery/2020-11/image-1604935159991.png) [](https://doc.gecloud.ch/uploads/images/gallery/2020-11/image-1604935178173.png) Description and Download of the Template here: [https://community.checkpoint.com/community/management/visibility-monitoring/blog/2018/04/04/threat-prevention-cyber-attacks-dashboard](https://community.checkpoint.com/community/management/visibility-monitoring/blog/2018/04/04/threat-prevention-cyber-attacks-dashboard) # DOS & DDOS Prevention, Mitigation ### Preface Since R80.20 DOS/DDOS Prevention changed in Check Point. The following is a summary how you can setup and mitigate DOS & DDOS attacks. #### SYN Defender since R80.20 ##### Important changes in IPS "SYN Attack" (SYN Defender) protection for R80.20 and above [https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit\_doGoviewsolutiondetails=&solutionid=sk120476](https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=sk120476) ##### How to configure Rate Limiting rules for DoS Mitigation (R80.20 and newer) [https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit\_doGoviewsolutiondetails=&solutionid=sk112454](https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=sk112454) #### Mitigation ##### How to configure Security Gateway to detect and prevent port scan [https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit\_doGoviewsolutiondetails=&solutionid=sk110873&partition=Advanced&product=Security](https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=sk110873&partition=Advanced&product=Security) ##### How to create and view Suspicious Activity Monitoring (SAM) Rules [https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit\_doGoviewsolutiondetails=&solutionid=sk112061](https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=sk112061) #### Best practice - Set "Host Scan" and "Sweep Scan" in IPS Policy to "User Alert 1". - In Global Settings on Smartcenter at "User Alert 1" 120 seconds blocking of source ip run via script `sam_alert -t 120 -I -src` # Export Syslog Messages ### Export Syslog Messages How to export syslog messages from Gaia Security Gateway to a Log Server and view them in SmartView Tracker [https://supportcenter.checkpoint.com/supportcenter/portal?action=portlets.SearchResultMainAction&eventSubmit\_doGoviewsolutiondetails=&solutionid=sk102995](https://supportcenter.checkpoint.com/supportcenter/portal?action=portlets.SearchResultMainAction&eventSubmit_doGoviewsolutiondetails=&solutionid=sk102995) ### Syslog from LOM InterfaceAt the moment it seems that syslog cannot be sent from Check Point LOM Interface.
# Missing feature - Global search across multiple CMA ### Preface Before R80.x in a MDM (Multi Domain Management) you could do a search where an object is used in all the CMA's. Until now (R80.30) this feature is not included in SmartConsole anymore. #### Script solution - [https://github.com/WadesWeaponShed/Global-IP-Search-MDS](https://github.com/WadesWeaponShed/Global-IP-Search-MDS) - [https://community.checkpoint.com/t5/API-CLI-Discussion-and-Samples/MDS-Global-search-across-CMAs-by-IP/m-p/75906](https://community.checkpoint.com/t5/API-CLI-Discussion-and-Samples/MDS-Global-search-across-CMAs-by-IP/m-p/75906) - [https://community.checkpoint.com/t5/API-CLI-Discussion-and-Samples/Search-multiple-CMA/m-p/35237](https://community.checkpoint.com/t5/API-CLI-Discussion-and-Samples/Search-multiple-CMA/m-p/35237) #### The Script ```shell #!/bin/sh JQ=${CPDIR}/jq/jq OBJECT_NAME=$1 DOMAINS_FILE="domains.json" PACKAGES_FILE="packages.json" PACKAGE_FILE="package.json" echo 'Getting a list of domains...' mgmt_cli -r true -d MDS show domains limit 500 --format json > $DOMAINS_FILE if [ $? -eq 1 ]; then echo "Error getting list of domains. Aborting!" exit 1 fi DOMAINS_NAMES=($($JQ -r ".objects[] | .name" $DOMAINS_FILE)) echo 'Searching for object '"$OBJECT_NAME"' in all domains...' FOUND=0 OBJECT_UID="" for DOMAIN in ${DOMAINS_NAMES[@]} do echo 'Searching in domain '"$DOMAIN"'...' mgmt_cli -r true -d "$DOMAIN" show objects offset 0 limit 1 in.1 name in.2 "$OBJECT_NAME" --format json > $OBJECT_NAME.json if [ $? -ne 1 ]; then OBJECT_COUNT=$($JQ -r ".total" $OBJECT_NAME.json) if [ $OBJECT_COUNT -ne 0 ]; then FOUND=1 OBJECT_UID=$($JQ -r ".objects[0].uid" $OBJECT_NAME.json) echo 'Found in domain '"$DOMAIN"'!!!' break fi fi done if [ $FOUND -ne 1 ]; then echo 'Object '"$OBJECT_NAME"' does not exist. Aborting!' exit 1 fi echo 'Searching for object '"$OBJECT_NAME"' usages in all policy packages in all domains...' for DOMAIN in ${DOMAINS_NAMES[@]} do echo 'Searching in domain '"$DOMAIN"'...' mgmt_cli -r true -d "$DOMAIN" show packages limit 500 --format json > $PACKAGES_FILE if [ $? -ne 1 ]; then PACKAGES_NAMES=($($JQ -r ".packages[] | .name" $PACKAGES_FILE)) for PACKAGE in ${PACKAGES_NAMES[@]} do echo 'Searching in package '"$PACKAGE"'...' mgmt_cli -r true -d "$DOMAIN" show-package name $PACKAGE --format json > $PACKAGE_FILE if [ $? -ne 1 ]; then ACCESS_LAYERS=($($JQ '.["access-layers"][] | .name' -r $PACKAGE_FILE)) for LAYER in ${ACCESS_LAYERS[@]} do mgmt_cli -r true -d "$DOMAIN" show access-rulebase package "$PACKAGE" name "$LAYER" offset 0 limit 1 filter $OBJECT_UID --format json > $OBJECT_NAME.json if [ $? -ne 1 ]; then OBJECT_COUNT=$($JQ -r ".total" $OBJECT_NAME.json) if [ $OBJECT_COUNT -ne 0 ]; then echo 'The requested object is used in policy package '"$PACKAGE" break fi fi done fi done fi done echo 'Done!' ``` # Show logging using the web interface If you need to view Logs over the Web in Check Point you can use SmartView. Available since R80 but not enabled per default. In R80.10 it is enabled per default and you can access it with your SmartConsole Credentials. It looks like this in the Browser: [](https://doc.gecloud.ch/uploads/images/gallery/2020-11/image-1604935250608.png) Also see here: [https://community.checkpoint.com/thread/5212-smartview-accessing-check-point-logs-from-web](https://community.checkpoint.com/thread/5212-smartview-accessing-check-point-logs-from-web) # Managing partition sizes via LVM manager on Gaia OS ### Partition Resize Since R77.30 *lvm\_manager* is included in Gaia OS and can be used to resize logical volumes on the system. Check [Managing partition sizes via LVM manager on Gaia OS (sk95566)](https://supportcenter.checkpoint.com/supportcenter/portal?action=portlets.SearchResultMainAction&eventSubmit_doGoviewsolutiondetails=&solutionid=sk95566) for more information. ### Partition Sizes when installing Gaia OS When instaling Gaia OS there is an option to change the partition sizes. Don't use default sizes as they are for minimal usage. Screenshot: 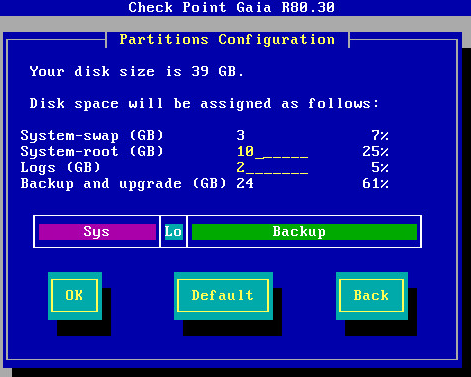 Check this Link: [How to configure partition sizes during Gaia installation (sk92303)](https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=sk92303) # SmartConsole cli parameters In R77.30 you could use command line parameters to specify username/password like this: `FwPolicy.exe connect %Hostname% %Username%` Since R80.10 you need to do the following: `SmartConsole.exe -p SmartConsole.LoginParams` Here is the SmartConsole.LoginParams example file: ```XMLFor non-mds connection you need to leave "DomainName" field empty.
Link: [https://community.checkpoint.com/thread/6432-command-line-arguments-to-r8010-smartconsoleexe](https://community.checkpoint.com/thread/6432-command-line-arguments-to-r8010-smartconsoleexe) # Jump to Rule Number or UID In R80.10 you can jump directly to a rule number or a rule-UID. With Ctrl-G you get the following: [](https://community.checkpoint.com/servlet/JiveServlet/showImage/2-9418-59540/2+enter+number.png) You can copy the UID from a rule:  Or search for an rule-UID: 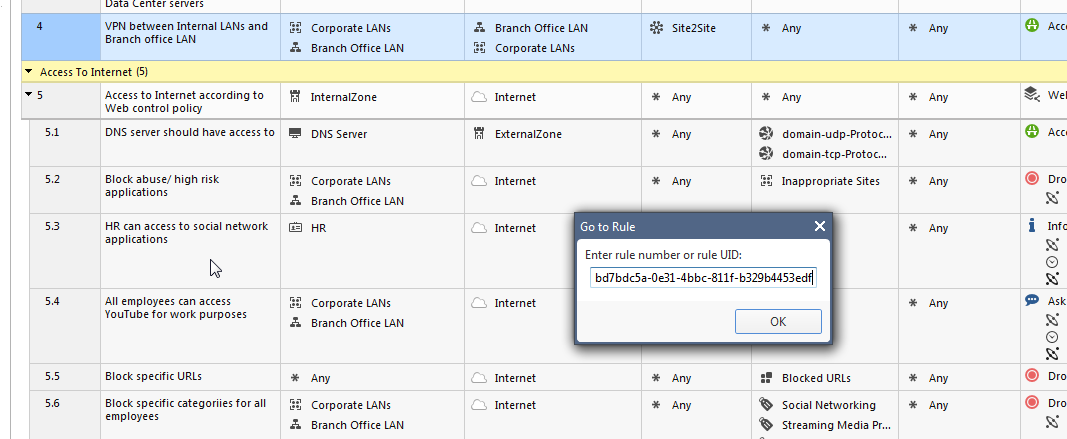 Perfect to use in documentations, just use the rule-UID or sometimes I also use the <FW\_RuleName: FW\_RuleName> Tag for documentation. # SmartConsole: Clear disconnected sessions ### Howto clear disconnected sessions If several SmartConsole disconnected (stale) sessions that cannot be discarded, see this here: [https://community.checkpoint.com/t5/General-Management-Topics/clear-disconnected-sessions/td-p/33027](https://community.checkpoint.com/t5/General-Management-Topics/clear-disconnected-sessions/td-p/33027) #### Postgresql Queries ##### View ```shell psql_client cpm postgres -c "select applicationname,objid,creator,state,numberoflocks,numberofoperations,creationtime,lastmodifytime from worksession where state = 'OPEN' and (numberoflocks != '0' or numberofoperations != '0');" ``` ##### Clear ```shell mgmt_cli discard --port 4434 uid 4b2ac7a8-9b0b-4e39-a3f0-4c065d631cdf Username: admin Password: number-of-discarded-changes: 2 message: "OK" ``` # Initiating manual cluster failover This command lets you initiate a manual cluster failover (see [sk55081](https://supportcontent.checkpoint.com/solutions?id=sk55081)). ### Syntax| Shell | Command |
|---|---|
| Gaia Clish | `set cluster member admin {down | up}` |
| Expert mode | `clusterXL_admin {down | up}` |